Cyber Insurance Guide for Businesses: Risk Management 2026
Introduction to the 2026 Cyber Risk Ecosystem
As the global digital economy transitions deeper into the artificial intelligence era, the intersection of cybersecurity and financial risk transfer has never been more critical. In 2026, the cyber insurance market is defined by a complex and costly paradox. Global cybersecurity spending has reached unprecedented levels, projected by industry analysts to hit $240 billion, representing a 12.5% year-over-year increase from 2025. Concurrently, the global cyber insurance market has achieved a valuation of approximately $22.5 billion, with projections suggesting a climb toward $29 billion by 2027. Yet, despite these massive investments in defensive infrastructure and risk transfer mechanisms, businesses are experiencing cyber incidents with greater frequency than ever before. Organizations are now twice as likely to suffer a cyber incident compared to five years ago, signaling that the mere accumulation of security software—the so-called “Cyber Protection Paradox”—is insufficient to guarantee organizational resilience.
The cyber insurance sector, however, has proven to be an oasis of stability amidst this turbulence. Following a period of aggressive market hardening between 2020 and 2022, the environment in 2026 is decidedly buyer-friendly. Increased insurer capacity, bolstered by strong reinsurance participation and improved cybersecurity maturity among insureds, has driven global premium pricing down by approximately 7%. This softening of premiums masks a highly sensitive market environment where the frequency of claims has surged by nearly 40% in the United States alone, surpassing 50,000 reported claims annually. Insurers are responding not by restricting capacity, but by mandating strict, verifiable security controls and utilizing artificial intelligence to refine their underwriting analytics.
For digitally native operations—specifically digital marketing agencies and e-commerce platforms—this landscape presents unique existential threats. The digitization of the consumer journey, coupled with the rapid adoption of generative AI, has expanded the attack surface exponentially. Threat actors are deploying sophisticated techniques ranging from AI-powered deepfakes and automated phishing campaigns to highly targeted supply chain intrusions and digital skimming operations. Simultaneously, regulatory frameworks are tightening globally, shifting liability directly onto the shoulders of corporate leadership and penalizing unauthorized data collection with draconian fines.
This comprehensive report provides an exhaustive analysis of the cyber insurance and risk management landscape in 2026. It meticulously evaluates the evolving threat vectors, dissects the stringent new regulatory and compliance mandates (including the now-mandatory PCI DSS v4.0), and provides a comparative analysis of the leading cyber liability policies designed specifically for digital agencies and e-commerce stores.
Macro-Market Dynamics and Evolving Threat Vectors
Understanding the cyber insurance market requires a granular examination of the primary severity drivers that are reshaping underwriting models and claim payouts in 2026. While the market remains well-capitalized and broadly profitable, insurers are hyper-focused on systemic accumulation risks, particularly widespread cloud provider outages, core technology vendor failures, and AI-enabled financial fraud.
The Evolution of Ransomware: From Encryption to Exfiltration
Ransomware continues to be the dominant driver of cyber insurance underwriting considerations, accounting for 44% of reported breaches and an overwhelming 81% of business interruption claims. The financial scale of these events is staggering, with average ransom demands surging by 47% to approximately $1.1 million, and the largest recorded demands eclipsing $150 million.
However, a critical behavioral shift has occurred within the threat actor ecosystem. Improved backup controls, immutable storage, and resilient network architectures have empowered 86% of affected businesses to outright refuse to pay ransom demands. In response, cybercriminals have pivoted from simple encryption tactics to complex data extortion. In 2026, 70% of ransomware events involve the exfiltration of sensitive data alongside encryption. This dual-threat approach effectively doubles the total cost of the incident. Organizations must now navigate devastating privacy liability claims, regulatory investigations, and third-party litigation, even if they possess the capability to restore their systems independently from backups. Consequently, while total ransomware payments have seen a slight decline from $892 million in 2024 to $820 million in 2025, the severity and complexity of individual loss events have intensified.

Social Engineering and Business Email Compromise (BEC)
Despite the technological sophistication of modern attacks, human error remains the most heavily exploited vulnerability. Social engineering, specifically Business Email Compromise (BEC) and Funds Transfer Fraud (FTF), constitutes the highest frequency of all cyber insurance claims. Phishing and spoofing attacks account for 58% of all claims, with 71% of FTF claims directly resulting from social engineering.
The financial toll of these attacks is substantial. BEC-related losses have totaled approximately $2.77 billion globally, with the average single incident costing organizations between $75,000 and $112,000. The proliferation of artificial intelligence has poured gasoline on this threat vector. AI-generated phishing lures have increased click-through rates by up to 54%, seamlessly eliminating traditional red flags such as poor grammar and spelling anomalies. Furthermore, deepfake technology is increasingly weaponized to mimic executives or vendors via audio and video, exploiting visual trust to bypass internal payment verification controls and amplifying exposure to financial fraud.
The Business Interruption Crisis
When liability is absent from a claim, Business Interruption (BI) emerges as the single largest driver of claim severity. Claims involving BI are, on average, 650% more costly than non-BI claims. The average BI loss for small and mid-sized enterprises (SMBs) has escalated sharply from $611,000 in 2024 to over $1 million in 2025 and 2026.
This sharp increase reflects a growing reliance on complex digital infrastructure across all industries, resulting in longer downtime when systems are compromised. A major friction point within the insurance industry is the time required to calculate and pay BI claims, which often takes more than a year to evaluate and settle, leaving businesses starved of operational capital during the recovery phase.
Sector-Specific Breach Severity
Actuarial models in 2026 must reconcile the global average data breach cost of $4.44 million to $4.88 million against the significantly elevated United States average, which now exceeds $10.22 million. This geographical disparity forces insurers to apply aggressive territorial multipliers when underwriting U.S.-based operations. Costs also vary wildly depending on the targeted industry, reflecting the intrinsic value and regulatory sensitivity of the data housed within those sectors.
| Industry Sector | Average Data Breach Cost (USD) | Implication for Underwriting |
|---|---|---|
| Healthcare | $10.93 Million | Highest regulatory scrutiny; high individual record value. |
| Financial Services | $5.90 Million | Prime target for direct FTF and systemic extortion. |
| Technology / SaaS | $4.66 Million | High third-party supply chain risk and Tech E&O exposure. |
| Professional Services | $4.47 Million | Vulnerable to BEC, invoice manipulation, and client data loss. |
| Retail / E-commerce | $2.96 Million | Frequent target of high-volume digital skimming and DDoS. |
The Regulatory Crucible: Privacy, Compliance, and Liability
The regulatory environment in 2026 is fraught with peril for organizations that handle consumer data. Regulators are broadening their enforcement mandates far beyond traditional data breaches involving credit cards or Social Security numbers. Enforcement now targets evolving data practices, including biometric data collection, facial recognition technology, behavioral tracking, and AI-driven profiling.
The Weaponization of Privacy Statutes
The California Invasion of Privacy Act (CIPA), a statute originally drafted in 1967, has been effectively weaponized by plaintiffs’ attorneys to target modern web-tracking tools utilized by virtually all digital agencies and e-commerce stores. In recent analyses of cyber claims, 72% of privacy claims cited CIPA, with 11% of violations specifically targeting the use of the Meta Pixel and alleging the improper, unauthorized sharing of consumer data with third parties.
Furthermore, state-level legislation such as the California Consumer Privacy Act (CCPA) and the California Privacy Rights Act (CPRA) introduce mandatory cybersecurity audits and risk assessments. These mandatory disclosures actively serve as key documents during litigation. For example, under California’s SB 446 (amending CA Civil Code §1798.82), businesses must notify residents within 30 calendar days of breach discovery. If a breach affects more than 500 residents, the Attorney General must be notified within 15 days of consumer notification, triggering immediate civil penalties and enforcement actions if non-compliance is detected.
International Governance and Executive Accountability
In Europe, the NIS2 Directive has fundamentally altered corporate risk profiles by shifting accountability directly to the C-suite.
Under NIS2, senior management can be held personally liable for failing to implement adequate human-centric security controls, eliminating the era where data breaches could be written off as unavoidable technical failures. Similarly, the EU’s Artificial Intelligence Act imposes stringent requirements on high-risk AI systems, with penalties for non-compliance reaching up to 7% of global revenue. Insurers are responding to these international shifts by reassessing policy language, often narrowing coverage around wrongful or unlawful data collection to limit their exposure to massive regulatory fines.
E-Commerce Specific Exposures: Magecart, DDoS, and Supply Chain Vulnerabilities
E-commerce operations represent one of the most lucrative targets for global cybercrime syndicates, bearing the brunt of 22% of all targeted Distributed Denial of Service (DDoS) attacks globally. While a DDoS attack is inherently disruptive, threat actors in 2026 frequently deploy them as a smokescreen, using botnets capable of unleashing record attacks peaking at 29.7 Tbps to mask deeper system intrusions. Beyond these brute-force tactics, e-commerce platforms must navigate highly specific, existential threats related to digital skimming.
Magecart and Digital Skimming Mechanics
E-commerce storefronts are under relentless assault from Magecart operations—a blanket term encompassing various criminal groups that specialize in injecting malicious JavaScript into online checkout pages to harvest payment card data. These digital skimming attacks exploit vulnerabilities in the e-commerce supply chain, often bypassing the primary security of the merchant by compromising third-party scripts, plugins, or cloud-based ConnectPOS software.
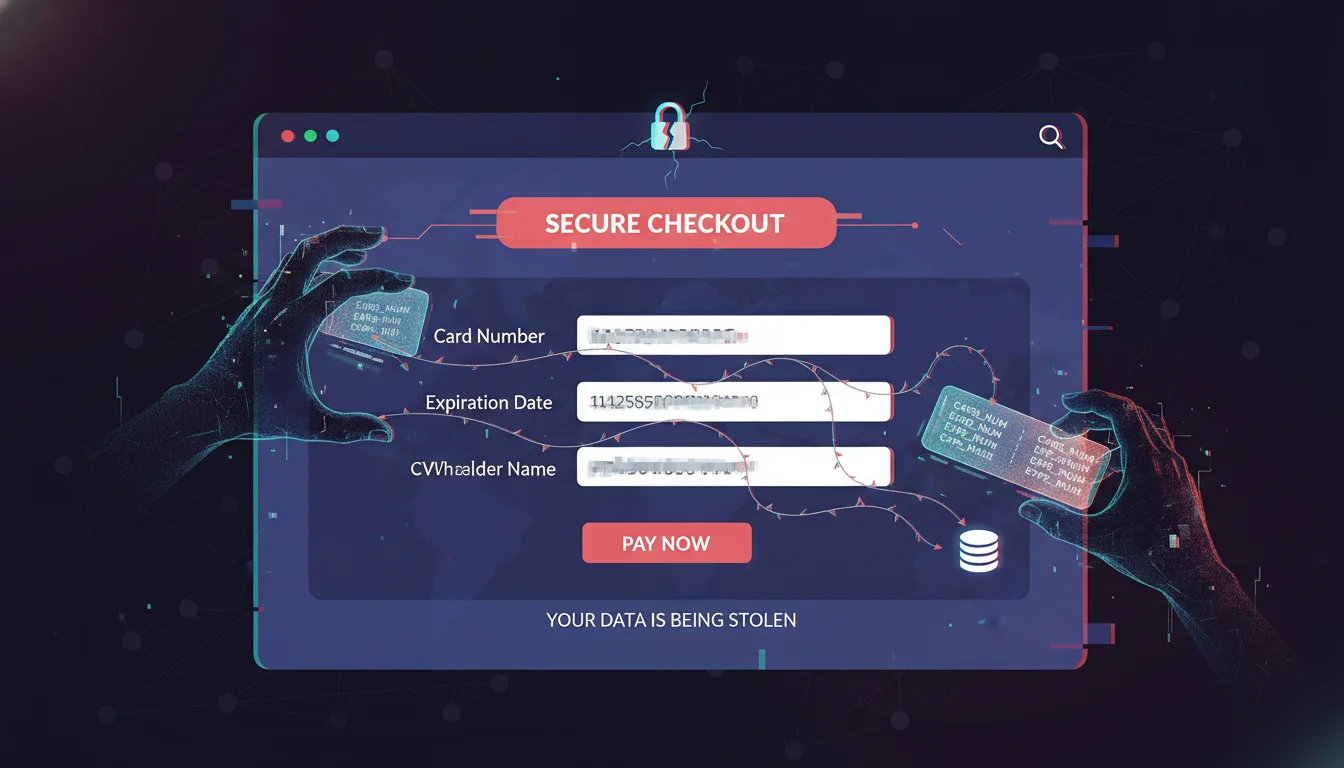
Recent threat intelligence highlights long-running campaigns specifically designed to infiltrate online shops utilizing the popular WooCommerce platform alongside Stripe payment gateways. The malicious JavaScript is heavily obfuscated and designed to detect and target specific card networks, including American Express, Discover, Mastercard, and UnionPay. Because the malicious code triggers only when a consumer enters their card details, and often includes self-destruct routines to evade detection by administrative sessions, these breaches can dwell undetected for months. The resultant theft triggers catastrophic liability for the e-commerce operator, initiating a cascade of forensic investigations, consumer notifications, and severe financial penalties.
Supply Chain Accumulation Risk
E-commerce heavily relies on interconnected APIs, cloud hosting (e.g., AWS, Azure), and SaaS operational tools. SecurityScorecard’s 2026 analysis indicates that cross-industry software vulnerabilities cause 37% of breaches, highlighting that even well-defended e-commerce platforms can be compromised through their lower-scoring supply chain partners. Indeed, third-party involvement in breaches has doubled, increasing from approximately 15% to 30%, forcing cyber insurers to heavily scrutinize the accumulation risk posed by systemic reliance on a core group of technology providers.
PCI DSS v4.0 and E-Commerce Cyber Insurance Selection
The Payment Card Industry Data Security Standard (PCI DSS) establishes the global baseline for safeguarding consumer financial data. As of April 2026, PCI DSS v4.0 is strictly mandatory; there are no remaining grace periods, and legacy versions of the standard have been retired. For e-commerce businesses, v4.0 fundamentally alters both the technical requirements of operations and the realities of securing cyber insurance.
Critical Technical Mandates Under v4.0
Version 4.0 introduces rigorous new mandates explicitly designed to counter Magecart-style attacks and credential theft.
- Payment-Page Script Security: Requirement 6.4.3 mandates that businesses maintain a justified, documented inventory of every client-side script running on payment pages. Each script must be authorized and its purpose documented. Furthermore, Requirement 11.6.1 necessitates the implementation of active tamper and change detection systems on payment pages, generating immediate alerts for any unauthorized modifications.
- Expanded Multi-Factor Authentication (MFA): Requirement 8 expands the scope of MFA, mandating it for all access paths into the Cardholder Data Environment (CDE), including third-party vendors and all privileged access—not just remote or administrative access.
- Password Length and Complexity: The minimum password length has increased to 12 characters for systems in scope.
- Targeted Risk Analysis (TRA): Organizations must now use a risk-based methodology to document and justify the frequency of their security scans and reviews, rather than relying on fixed activity schedules.
Underwriting and Carrier-Ready Evidence
From an insurance perspective, underwriters in 2026 no longer accept simple attestations of compliance via self-assessment questionnaires. Carriers demand documented, live proof of PCI controls. E-commerce businesses must provide a “Carrier-Ready Evidence Pack” containing MFA enforcement screenshots, payment-page script inventories, completed TRA templates, and CDE diagrams showing data flows and segmentation. Organizations that produce this evidence move through underwriting faster, secure superior premium pricing, and avoid coverage denials during the claims evaluation process.
The Financial Architecture of PCI Compliance and Penalties
Maintaining compliance is inherently expensive, but the cost of non-compliance following a breach is ruinous. Annual PCI compliance costs vary dramatically based on the merchant’s transaction volume.
| Merchant Level | Transaction Volume | Assessment Type Required | Estimated Annual Compliance Cost |
|---|---|---|---|
| Level 1 | > 6 million transactions/yr | Report on Compliance (ROC) by QSA | $50,000 – $500,000+ |
| Level 2 | 1-6 million transactions/yr | SAQ + quarterly ASV scans (QSA optional) | $10,000 – $50,000 |
| Level 3 | 20k - 1M e-commerce trans. | SAQ + quarterly ASV scans | $5,000 – $20,000 |
| Level 4 | < 20,000 e-commerce trans. | SAQ (type depends on acceptance method) | $1,000 – $5,000 |
If an e-commerce platform suffers a breach and is found non-compliant with v4.0 controls, cyber insurers will heavily scrutinize the claim, potentially denying the payout. The business is then left to absorb catastrophic liabilities imposed by acquiring banks and card brands.
| Liability Component | Estimated Cost Range | Implication for E-Commerce |
|---|---|---|
| PCI Forensic Investigation (PFI) | $20,000 – $100,000 | Mandatory third-party investigation ordered by card brands. |
| Card Brand Fines | $50,000 – $500,000 | Punitive fines for failing to secure the CDE. |
| Card Replacement Costs | $3 – $10 per card | Hard costs to reissue compromised physical plastic. |
| Regulatory Fines (State/Federal) | $10,000 – $1,000,000+ | AG enforcement and potential Federal Trade Commission action. |
| Class Action Settlements | $1,000,000 – $100,000,000+ | Consumer litigation for negligence in data handling. |
When selecting a cyber insurance policy, e-commerce stores must ensure the policy includes specific endorsements for PCI Fines and Assessments, which covers the expenses to defend against and pay PCI fines arising from a data breach. Without this specific endorsement, the standard third-party liability agreement will likely exclude contractual card brand fines.
Digital Agencies: Navigating Third-Party Risk and Media Liability
Digital agencies—encompassing marketing, advertising, public relations, and software development firms—operate at a unique intersection of data management and content creation. Their risk profiles are inherently complex. They not only maintain highly sensitive client data, such as strategic marketing budgets, intellectual property, and proprietary CRM access, but they also generate massive volumes of public-facing digital media. Consequently, standard first-party cyber policies are wholly inadequate; digital agencies require robust third-party liability modules to protect against client lawsuits.
Media Liability and Intellectual Property Exposures
In the modern digital agency, content is deployed across websites, social media, blogs, and interactive campaigns at breakneck speeds. This rapid deployment is increasingly augmented by generative AI tools, which, while boosting efficiency, create severe media liability exposures. Digital agencies are highly susceptible to claims of copyright and trademark infringement, libel, slander, defamation, and improper deep linking.
The use of third-party influencers further amplifies this risk, as agencies can be held vicariously liable for the actions, statements, or copyright violations committed by the content creators they manage. Comprehensive cyber policies for digital agencies must include explicit “Media Liability” or “Multimedia Content Liability” endorsements to provide legal defense and indemnity for these specific wrongful acts. Without this, an AI-generated image that inadvertently infringes on a copyrighted asset could result in uncovered litigation.
Technology Errors and Omissions (Tech E&O)
Digital agencies that provide IT consulting, web design, or software-as-a-service (SaaS) architecture face intense scrutiny regarding the efficacy of their deliverables. If a digital agency builds an e-commerce platform for a client that subsequently suffers a Magecart attack due to a faulty plugin implementation or poor firewall configuration, the client will undoubtedly sue the agency for financial damages.
Technology Errors and Omissions (Tech E&O) coverage is a non-negotiable requirement for these firms.
It provides defense costs and damages arising from third-party liability when the failure of the agency’s technology service, product, or consultation is the proximate cause of the client’s financial loss. Often, comprehensive policies seamlessly blend Tech E&O with standard cyber liability to ensure there are no gaps in coverage when an operational error directly leads to a network security failure.
The Danger of Client Impersonation and Invoice Manipulation
Digital agencies handle significant financial throughput, frequently managing high-value media purchasing budgets on behalf of their clients. This makes them prime targets for sophisticated social engineering. Threat actors routinely compromise agency email servers to observe communications, eventually intercepting vendor invoices and altering the routing numbers to divert funds.
Insurance policies for agencies must include robust “Cyber Crime” modules, specifically covering Funds Transfer Fraud, Social Engineering, and Invoice Manipulation. Invoice Manipulation coverage is particularly vital; it reimburses the agency for direct net costs if they are unable to collect payment because their client was tricked by a threat actor into sending the agency’s rightful payment to a fraudulent account.
Comparative Carrier Analysis for Digital Operations
The cyber insurance marketplace in 2026 is populated by highly sophisticated carriers, but their appetites, policy structures, and target demographics vary significantly. Selecting the appropriate carrier is a strategic exercise that dictates an organization’s survival post-breach. An exhaustive comparative analysis of the primary carriers—Chubb, Coalition, Hiscox, Travelers, and AIG—revels distinct strategic advantages for different business archetypes.
Chubb: The Comprehensive Enterprise Powerhouse
Chubb maintains its position as the premier global insurer, achieving unparalleled financial strength ratings, including an “AA” (Very Strong) from Standard & Poor’s and an “A++” (Superior) from A.M. Best.
- Target Market: Businesses of all sizes, though Chubb is particularly dominant in the mid-market to large enterprise space requiring complex, multi-national coverage and regulatory compliance.
- Coverage Strengths: Chubb is universally praised for its claims reliability, exceptional coverage depth, and rapid claims processing. Its Cyber Enterprise Risk Management (ERM) policy provides seamless integration of first-party breach response, Tech E&O, and Media Liability, making it an excellent fit for complex digital agencies. Furthermore, Chubb offers a Cyber Facility for organizations over $1 billion in revenue that require substantial primary limits to build large insurance tower programs.
- Global Reach: The carrier’s infrastructure supports operations in over 35 countries natively, providing localized incident response teams and multinational program structuring.
Coalition: The Active Insurance Disruptor
Coalition has fundamentally transformed the market through its “Active Insurance” methodology, moving beyond reactive financial indemnity to proactive threat mitigation and continuous monitoring.
- Target Market: Tech-forward businesses, high-risk SaaS platforms, digital agencies, and e-commerce platforms that value real-time risk management and rapid digital asset restoration.
- Coverage Strengths: Coalition continuously scans policyholder networks for vulnerabilities, integrating proprietary technology (such as Coalition Control and Wirespeed MDR) to intercept threats before they materialize. This approach yields extraordinary results: in 2025, 64% of closed claims resulted in zero out-of-pocket loss for the policyholder. Their specialized incident response teams successfully negotiated ransom payments down by an average of 65% and recovered $21.8 million in stolen funds (averaging $202,000 per incident). They also offer comprehensive Tech E&O and Media Liability modules perfectly suited for agencies.
- Global Reach: Coalition has aggressively expanded its international footprint. As of 2026, it offers comprehensive admitted and surplus lines in all 50 U.S. states, all Canadian provinces, the United Kingdom, Australia, and Germany.
Hiscox: The SMB and Media Liability Specialist
Hiscox, an Anglo-Bermudan insurer and constituent of the FTSE 100 Index, caters aggressively to the specific operational realities of small and medium-sized businesses (SMBs), including independent digital agencies and boutique e-commerce shops.
- Target Market: Budget-conscious founders, early-stage startups, consultants, and media-heavy small businesses looking for flexible, streamlined coverage.
- Coverage Strengths: Hiscox is lauded for its highly flexible, digital-first policy management and industry-leading protections against cybercrime and social engineering. For digital agencies, Hiscox provides highly tailored Media Liability modules protecting against copyright infringement and advertising injury.
- Cost Efficiency: Hiscox offers aggressive entry-level pricing, with base policies starting as low as $30 per month. They also offer bundling discounts (up to 5%) when combining cyber liability with a Business Owner’s Policy (BOP). However, prospective buyers must note that Hiscox policies explicitly exclude biometric data claims and infrastructure utility failures, which could be problematic for agencies utilizing advanced AI tracking.
Travelers and AIG: Niche Strategic Offerings
- Travelers: Highly rated for broad network security and privacy coverage, Travelers excels in pre-emptive threat prevention. It is the preferred carrier for risk-aware teams that require extensive pre-breach training resources, network privacy support, and robust business interruption modeling. Their CyberFirst Essentials policy is explicitly built to deliver data breach liability coverage for small businesses.
- AIG: AIG focuses its underwriting heavily on loss prevention and high-severity data breach incident management. Their policies are highly sought after by organizations seeking aggressive ransomware defense, deep legal defense assistance against regulatory bodies, and proactive risk consulting to manage threats before escalation.
Carrier Comparison Matrix for Digital Operations
| Carrier | Primary Target Market | Core Differentiators & Strengths | Global/Regional Reach | Best Suited For |
|---|---|---|---|---|
| Chubb | All sizes, Mid-Enterprise | Deep coverage depth, superior claims reliability, financial strength (A++), capable of $1B+ revenue limits. | Global (35+ countries). | Regulated SaaS, global agencies, complex e-commerce platforms. |
| Coalition | Tech-forward SMBs/Mid | Active monitoring, $0 out-of-pocket for 64% of claims, FTF recovery, Tech E&O. | US, UK, Canada, Australia, Germany. | Digital agencies, highly targeted e-commerce. |
| Hiscox | Small Businesses / Startups | Affordability ($30/mo base), strong media liability, social engineering protection. | US (49 states), Europe. | Boutique marketing agencies, budget-conscious founders. |
| Travelers | Small to Mid-Sized | Pre-emptive threat prevention, extensive training tools, CyberFirst Essentials. | US Domestic focused. | Risk-aware teams wanting deep educational support. |
| AIG | Mid to Large Enterprise | Legal defense superiority, ransomware negotiation, proactive consulting. | Global. | High-risk environments requiring heavy compliance defense. |
Financial Architecture: Pricing Models, Limits, and Deductibles
The financial modeling of cyber risk involves a careful calculus between premium expenditures, self-insured retentions (deductibles), and the realistic aggregate costs of a potential breach. Small and mid-sized businesses frequently underestimate the total economic devastation of a cyber event, assuming that basic general liability or standard property policies will respond—an assumption that invariably leads to insolvency.
Benchmarking the Total Cost of an SMB Breach
When a mid-sized digital agency or e-commerce platform suffers a breach, the direct, out-of-pocket costs materialize across several distinct categories well before a ransomware payout is even negotiated. The following table illustrates the typical expense range an SMB faces during an incident:
| Cost Category | Typical Range (SMB) | Contextual Driver |
|---|---|---|
| Forensic Investigation | $15,000 – $50,000 | External cybersecurity teams required to determine entry vectors and data scope. |
| Legal Fees and Counsel | $20,000 – $75,000 | Breach coaches navigating 50 distinct state notification laws and federal statutes. |
| Customer Notification | $5,000 – $30,000 | Mandatory mailing, call center setup, and administrative outreach. |
| System Restoration | $10,000 – $100,000 | Rebuilding network architecture and recovering data from backups. |
| PR and Crisis Comms | $5,000 – $25,000 | Retaining specialists to stabilize brand reputation and client trust. |
| Regulatory Fines | $10,000 – $500,000+ | Penalties from HIPAA, PCI, or State AGs for compliance failures. |
| Business Interruption | $25,000 – $250,000+ | Lost revenue and extra expenses incurred while systems are offline. |
Collectively, the total baseline exposure for an SMB cyber incident ranges from $140,000 to well over $2,000,000, explicitly demonstrating the absolute necessity of robust policy limits.
Cyber Insurance Premium Pricing Models
Cyber insurance premiums in 2026 are highly dynamic, dictated by the organization’s industry risk tier, annual revenue, data volume, and the maturity of its internal security controls.
On a macro level, the average small business pays approximately $83 to $134 per month (roughly $999 to $1,609 annually) for a baseline cyber liability policy with a $1 million aggregate limit. However, organizations operating in high-risk sectors—such as e-commerce (handling vast amounts of PCI data) and digital agencies (holding third-party access and SaaS capabilities)—face steeper premium structures due to their elevated threat profiles.
| Industry Sector | Actuarial Risk Level | Average Annual Premium ($1M Limit) | Market Dynamics |
|---|---|---|---|
| Technology / SaaS / Agencies | High | $2,000 – $6,000 | Premiums elevated due to Tech E&O requirements and third-party network access risks. |
| Retail / E-commerce | Medium-High | $1,500 – $4,000 | Premiums driven by high-volume data collection, PCI exposure, and digital skimming threats. |
| Professional Services | Medium | $1,000 – $3,000 | Moderate risk, primarily exposed to BEC and standard social engineering. |
Deductible Structures and Behavioral Retentions
The deductible (or retention) is the financial threshold the insured must pay out-of-pocket before the insurance policy responds. For the average small-to-mid-sized digital agency or e-commerce store, deductibles typically range from $2,500 to $10,000. However, organizations can manipulate their premium costs by opting to bear more upfront risk. As operations scale, so do retentions; high-revenue enterprise policies frequently feature deductibles of $500,000.
Crucially, the market in 2026 is seeing a rise in behavioral deductibles. For instance, an organization may face a standard $1,000 deductible for a claim, but this amount can be punitively increased to $5,000 if the organization failed to conduct and document mandatory annual employee cybersecurity training prior to the incident.
The “3-Bucket” Sizing Method for Determining Limits
Purchasing a generic “$1 million policy” is often insufficient if the policy contains restrictive sublimits (e.g., capping ransomware payouts at $100,000). To accurately determine the necessary aggregate limits, risk managers must deploy the “3-Bucket Sizing Method”:
- Downtime Exposure: Calculate lost gross profit and the extra expenses required to restore operations manually over a standard 14-to-30 day outage.
- Data Exposure: Multiply the number of retained customer records by the average cost of notification, credit monitoring ($50 to $200 per record), and probable privacy liability litigation settlements.
- Third-Party Liability: Estimate the contractual liabilities owed to clients if the agency’s systems are used to propagate malware into a client’s network, or if an e-commerce platform exposes vendor data.
By quantifying these three buckets, organizations can ensure their base limits and sublimits accurately reflect their operational reality, ensuring robust protection against modern extortion mechanics.
Strategic Policy Procurement: Negotiating the Contract
Purchasing cyber insurance in 2026 requires meticulous scrutiny of policy wording. The difference between an agency surviving a catastrophic ransomware attack and entering liquidation often hinges on subtle definitions and sublimits buried deep within the policy architecture. Digital businesses must prioritize several critical selection criteria during procurement to ensure the policy performs as intended during a crisis.
Panel Selection and Choice of Professionals
A hidden friction point in cyber insurance claims is the carrier’s use of pre-approved “panel” providers. Most cyber policies stipulate that if a breach occurs, the insured must utilize forensic investigators, breach coaches, and legal counsel selected from the insurer’s proprietary list. Insurers use these panels to control costs by leveraging pre-negotiated hourly rates or fixed prices for certain investigations.
However, a digital agency or e-commerce store may already have an incident response (IR) firm on retainer that intimately understands its bespoke AWS architecture or proprietary code base. If the business uses its own non-panel IR firm during a crisis without prior authorization, the carrier can legally deny the indemnification of those costs. Organizations must negotiate with their brokers to have their preferred IT forensics and legal counsel explicitly added to the policy via endorsement before binding the coverage.
Navigating Problematic Exclusions
Insurers aggressively seek to limit their exposure to unquantifiable, systemic risks through policy exclusions. Buyers must audit policies for the following highly detrimental clauses:
- AI Exclusions: As digital agencies increasingly rely on generative AI, policies with broad AI exclusions may deny coverage if an AI tool was involved in a copyright infringement claim or if an AI-driven security filter failed to catch a phishing email.
- Widespread Event Exclusions: These clauses limit or negate coverage if a single vulnerability (e.g., a flaw in a globally ubiquitous software library or major cloud provider) affects thousands of businesses simultaneously, capping the insurer’s systemic loss but leaving the insured exposed.
- War Exclusions: Traditional war exclusions are increasingly being invoked by carriers to deny coverage for state-sponsored cyberattacks. Buyers must ensure they secure explicit “carvebacks” that preserve coverage for cyber-terrorism and collateral damage stemming from nation-state threat actors.
- Unencrypted Data Conditions: Some policies contain strict conditions precedent that nullify coverage entirely if the compromised data was not encrypted at rest. These clauses offer carriers an easy escape hatch during claims adjustments and should be rigorously avoided during negotiations.
Conclusion
The cyber risk ecosystem in 2026 presents an asymmetrical battleground where e-commerce stores and digital agencies face highly organized, AI-empowered adversaries alongside an increasingly punitive regulatory apparatus. The transition from simplistic ransomware encryption to devastating data exfiltration, coupled with the weaponization of outdated privacy statutes like CIPA, dictates that organizations can no longer rely on perimeter defense alone. The sheer volume of sophisticated threats guarantees that technical failures will occur, rendering comprehensive cyber liability insurance a fundamental pillar of corporate governance rather than a peripheral administrative expense.
For e-commerce operators, the uncompromising mandates of PCI DSS v4.0 demand continuous, documented technical vigilance to maintain insurability against crippling Magecart attacks and supply chain vulnerabilities. For digital agencies, the rapid proliferation of digital content and complex SaaS deliverables necessitates the seamless integration of Media Liability and Technology Errors & Omissions coverage alongside traditional network security modules.
The comparative strengths of market leaders highlight that there is no universal solution. Whether leveraging Chubb’s enterprise-grade stability and vast multinational capacity, Coalition’s proactive threat interdiction and extraordinary zero-out-of-pocket claims resolution rate, or Hiscox’s highly tailored flexibility for budget-conscious SMBs, businesses must actively align their specific technological footprint with precision-crafted insurance policies.
Resilience in the digital economy is achieved through meticulous preparation. By rigorously negotiating panel selections to include trusted incident response partners, eliminating predatory exclusions related to AI and widespread events, and fully quantifying their multi-tiered exposures utilizing the 3-Bucket Sizing Method, digital businesses can transform cyber insurance from a reactive safety net into a proactive, strategic asset. In doing so, they ensure uninterrupted operational continuity and safeguard their financial viability amidst the defining corporate threat of the decade.



