Stryker Cyber Attack Case Study: Identity Management Weaponized
Case Study: The March 2026 Stryker Corporation Cyberattack and the Weaponization of Enterprise Identity Management

Executive Summary
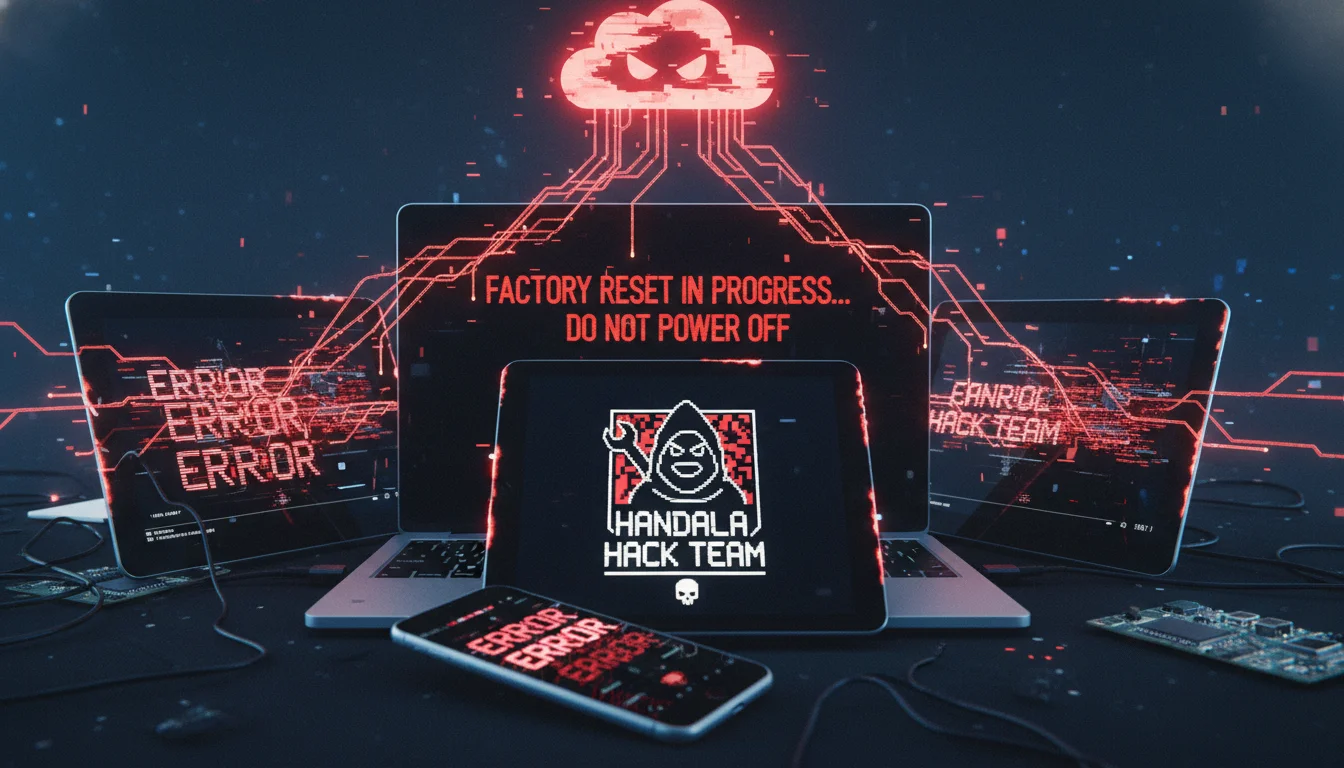
On March 11, 2026, the global digital infrastructure of Stryker Corporation—one of the world’s most prominent medical technology conglomerates—suffered a catastrophic, highly coordinated, and completely destructive cyberattack. This incident, which unfolded in the early hours of the morning on the United States East Coast, rapidly escalated from a covert network intrusion into a systemic “digital decapitation” that paralyzed the company’s internal networks, manufacturing hubs, and employee communications across the globe. Orchestrated by the Iran-linked hacktivist collective known as the Handala Hack Team, the attack dramatically deviated from the financially motivated ransomware campaigns that have historically plagued the global healthcare manufacturing sector. Instead of seeking financial extortion, the threat actors deployed sophisticated wiper malware designed explicitly to permanently obliterate corporate data across hundreds of thousands of enterprise endpoints, servers, and mobile devices.
The operational consequences of this breach were immediate, profound, and universally disruptive. Stryker, a Fortune 500 enterprise generating over $25 billion in annual revenue with a highly specialized workforce of approximately 56,000 employees spanning 61 countries, was forced to effectively halt its internal corporate operations. In major manufacturing, engineering, and administrative centers, most notably the company’s vast European hub in Cork, Ireland, thousands of employees were sent home as their workstations and personal mobile devices were remotely and maliciously factory-reset. The attack exploited foundational enterprise cloud management tools—specifically Microsoft Entra ID (formerly Azure Active Directory) and Microsoft Intune—transforming the very systems engineered to secure and manage the corporate fleet into a centralized, highly efficient mechanism for mass digital destruction.

This exhaustive research report investigates the multidimensional facets of the March 2026 Stryker cyberattack. It provides a granular, in-depth technical analysis of the initial access vectors, the unprecedented weaponization of cloud-based Mobile Device Management platforms, and the forensic architecture of the deployed wiper malware. Furthermore, the analysis explores the broader geopolitical dimensions of the attack, contextualizing Handala’s operations as an asymmetric, retaliatory measure directly linked to escalating kinetic conflicts between the United States, Israel, and the Islamic Republic of Iran. Finally, the report synthesizes the downstream implications for global medical supply chains, financial markets, and the future of enterprise cyber resilience in an era where cloud-based identity providers constitute a highly precarious single point of failure for multinational corporations.
Corporate Profile and the Systemic Vulnerability of Medical Manufacturing
To fully comprehend the magnitude, severity, and strategic logic of the March 2026 incident, it is essential to establish the systemic importance of the victim organization within the global healthcare ecosystem.
Stryker’s Role in the Global Healthcare Ecosystem
Headquartered in Portage, Michigan, Stryker Corporation is a dominant, foundational force in the global medical device and technology industry. With reported global sales revenues exceeding $25 billion in 2025 and $22.6 billion in 2024, the company operates as a critical supplier across three primary medical verticals: Orthopaedics, Medical and Surgical (MedSurg), and Neurotechnology. Stryker manufactures a highly diversified and technologically advanced portfolio of critical healthcare infrastructure. This ranges from joint replacement implants and emergency medical service (EMS) equipment, such as ambulance cots and life-saving defibrillators, to highly complex robotic surgical systems like the Mako Robotic-Arm Assisted Surgery platform.
The sheer scale of Stryker’s operations renders it a keystone entity in global health. The corporation employs approximately 56,000 people worldwide and serves an estimated 150 million patients annually, acting as an essential partner for hospitals, surgical centers, and emergency response teams. Its manufacturing and engineering footprint is highly globalized, with significant research, development, and production facilities located not only in the United States but heavily concentrated in Europe and Asia.
The Cork facility in Ireland serves as one of the company’s most critical and largest operational bases outside the United States. Employing upwards of 4,000 to 5,000 workers, the Cork campus is dedicated to advanced product engineering, manufacturing, and global supply chain logistics. When an entity of this size and scope is disrupted, the event ceases to be a mere corporate IT outage and elevates to the level of a critical infrastructure crisis.
Stryker Corporation Operational Profile
- Global Headquarters: Portage, Michigan, United States
- Major International Hub: Cork, Ireland (approx. 4,000 - 5,000 employees)
- Total Global Workforce: ~56,000 employees
- Global Reach: Operations in 61 countries; 79 global offices
- Annual Revenue: >$25 Billion ; $22.6 Billion
- Patient Impact: >150 Million patients served annually
- Core Product Verticals: Orthopaedics, MedSurg, Neurotechnology, Robotic Surgery (Mako)
The Convergence of IT Infrastructure and Medical Supply Chains
The modern healthcare manufacturing sector operates on a highly integrated, digitally dependent, and tightly optimized logistical model. The contemporary medical device supply chain relies heavily on complex Enterprise Resource Planning (ERP) systems, cloud-based collaboration tools, and connected digital manufacturing environments to maintain efficiency and meet clinical demand.
When a manufacturer of Stryker’s monumental scale is suddenly severed from its digital backbone, the production, quality assurance, regulatory compliance, and distribution of life-saving medical equipment are fundamentally jeopardized. Facilities that rely heavily on digitally connected production systems to build medical devices and surgical equipment cannot function when access to design software, production controls, and automated supply chain routing is revoked.
While medical devices already deployed in the field (such as hospital beds, defibrillators, and surgical robots currently in clinical settings) were not directly compromised or taken offline by the Handala cyberattack, the systemic disruption of the manufacturer introduces severe secondary and tertiary risks to patient care. Modern clinical technology is not static; it requires continuous vendor support, including device maintenance, critical software patches, cybersecurity vulnerability fixes, and logistical coordination for consumable surgical tools. The abrupt disruption of these essential support channels underscores a profound and systemic vulnerability: global healthcare infrastructure is inherently fragile, reliant on a continuous, uninterrupted umbilical cord of technical, software, and logistical support from upstream commercial manufacturers. The targeting of Stryker effectively weaponized this deep dependency, generating outsized strategic, economic, and political ripple effects across the global healthcare sector.
Geopolitical Catalyst and Threat Actor Attribution
The Stryker cyberattack cannot be analyzed in a vacuum; it is fundamentally a manifestation of geopolitical kinetic conflict spilling over into the digital domain. The attribution of the attack, the nature of the threat actor, and the explicit motivations provided by the attackers highlight the growing utilization of destructive cyber operations as a tool of asymmetric statecraft.
The Handala Hack Team: Architecture, Affiliation, and Capabilities
The attack on Stryker was rapidly claimed by, and subsequently attributed by cybersecurity researchers to, the “Handala Hack Team” (often referred to simply as Handala), a highly sophisticated pro-Palestinian and pro-Iranian hacktivist collective. Threat intelligence analysts, including those from Palo Alto Networks and other global security firms, have extensively tracked Handala, linking the group directly to the Islamic Republic of Iran’s Ministry of Intelligence and Security (MOIS). Specifically, Handala is identified as one of several online personas operated and maintained by the state-sponsored nexus known to researchers as Void Manticore.
Handala operates effectively as a “faketivist” front—a strategic, state-aligned construct designed to provide the Iranian government with a layer of plausible deniability while executing highly aggressive, overtly destructive, and deniable operations against international adversaries. Prior to the March 2026 Stryker incident, Handala had built a formidable operational resume characterized by advanced psychological warfare, high-volume data theft, and the deployment of custom wiper malware.
The group’s historical targets predominantly included Israeli critical infrastructure, military assets, financial institutions, and healthcare organizations.
Most notably, Handala previously claimed a massive data breach against Clalit, Israel’s largest healthcare network, which serves approximately half the country’s population. In that incident, Handala released sensitive medical data, including names, personal information, and details of medical screenings and tests for over 10,000 Israeli patients, declaring it a “devastating blow to the core of the Zionist regime’s healthcare system”. Furthermore, Handala has been implicated in wiping Israeli military weather servers, intercepting security feeds in Jerusalem, doxxing intelligence officers, and hacking oil and gas exploration companies.
Threat Actor Profile: Handala Hack Team
- Details
- Known Aliases: Handala Hack Team, Handala
- State Affiliation: Islamic Republic of Iran (Ministry of Intelligence and Security - MOIS)
- Associated Threat Nexus: Void Manticore
- Operational Persona: Pro-Palestinian / Pro-Iranian “Faketivist” Hacktivist Group
- Primary Motivation: Geopolitical retaliation, psychological warfare, systemic economic disruption
- Primary TTPs: Spear-phishing (Hebrew fluency), social engineering, massive data exfiltration, custom wiper malware deployment, MDM weaponization
- Historical Target Sectors: Healthcare (e.g., Clalit), Defense, Critical Infrastructure, Financial Services, Oil & Gas
The Broader Ecosystem of Iranian Cyber Warfare
Handala does not operate in isolation; it is part of a broader, highly coordinated ecosystem of Iranian-aligned cyber threat actors that leverage cyber operations to project power and retaliate against adversaries. The surge in pro-Iranian hacktivist activity provides the Iranian regime with the ability to project perceived power, especially during periods when domestic connectivity or kinetic military options are constrained.
Other notable groups operating within this sphere include:
- The FAD Team (Fatimiyoun Cyber Team): Composed of pro-regime actors who, like Handala, focus heavily on wiper malware and permanent data destruction, claiming attacks on SCADA/PLC systems in Israel.
- The Cyber Islamic Resistance: A pro-Iranian umbrella collective that coordinates multiple hacktivist teams (such as RipperSec and Cyb3rDrag0nzz) to launch synchronized DDoS attacks, data-wiping operations, and website defacements.
- Dark Storm Team and Evil Markhors: Groups specializing in large-scale DDoS, credential harvesting, and identifying unpatched critical systems across the Middle East.
The Catalyst: Asymmetric Retaliation for Kinetic Strikes
The timing and explicitly stated motive for the Stryker attack provide crucial context regarding the evolution of cyber warfare in contemporary geopolitical conflicts. On February 28, 2026, a joint United States and Israeli military operation resulted in a Tomahawk missile strike that hit an elementary school in Minab, Iran. Iranian state media and subsequent reports indicated that this strike resulted in the deaths of approximately 160 to 175 individuals, predominantly children.
In the immediate aftermath of this kinetic escalation, U.S. intelligence officials and federal security agencies issued stark warnings about the high probability of severe cyber retaliation from Tehran-linked threat actors targeting U.S. and Israeli infrastructure. Handala’s catastrophic attack on Stryker materialized roughly two weeks later, serving as a direct, asymmetric, and highly destructive response.
In a lengthy manifesto posted to their Telegram channel and various social media platforms on the day of the attack, the group explicitly stated that the operation was executed in direct retaliation for the Minab school strike. The group declared that the attack on Stryker was “only the beginning of a new chapter in cyber warfare,” framing their actions as retaliation for the “brutal attack” and ongoing cyber assaults against the infrastructure of the “Axis of Resistance”.
By targeting a $100 billion corporate entity that plays a critical role in Western healthcare infrastructure, Iranian proxies demonstrated a significant strategic shift. Rather than confining their operations to regional targets in the Middle East or Israeli domestic infrastructure, they sought to inflict maximum economic, operational, and psychological pain on high-profile United States corporate assets. The choice of a medical device manufacturer—a sector where human life and safety are tangentially but critically involved—amplifies the psychological terror and strategic pressure of the operation.
Attack Vector and Technical Chain of Compromise
The technical execution of the Stryker breach represents a masterclass in the abuse of centralized identity platforms and endpoint management architectures. While traditional ransomware operators typically rely on lateral movement, slow data encryption, and complex negotiation portals to extort victims, Handala optimized their attack path for instantaneous, irreversible destruction at a global scale.
Initial Access: Advanced Social Engineering and Spear-Phishing
While the precise patient-zero vulnerability or compromised account at Stryker remains actively under investigation by forensic teams, comprehensive threat intelligence surrounding Handala’s established methodologies points heavily toward highly targeted spear-phishing and advanced social engineering campaigns.
Handala does not merely rely on automated brute-forcing; they utilize sophisticated, context-aware lures. Within their phishing campaigns, the hacktivist group routinely masquerades as legitimate internal organizations, trusted vendors (such as cybersecurity firm CrowdStrike), or IT support teams offering solutions to known network issues. The threat actors take advantage of major global events, IT outages, or newly disclosed critical vulnerabilities to opportunistically craft phishing campaigns using advanced social engineering.
For example, threat intelligence from Cisco Talos indicates that Handala frequently uses spear-phishing attachments (MITRE ATT&CK T1566) containing deceptive links. An email might claim to offer a “fix tool” to resolve a Blue Screen of Death (BSOD) problem. When the victim clicks the embedded URL within the PDF or email, it directs them to malicious software that serves as the initial dropper for the group’s deeper intrusions or wiper payloads. Furthermore, Handala is known for the linguistic sophistication of their attacks; analysts assess with moderate confidence that members of the group are fluent in Hebrew, allowing for highly convincing, well-crafted emails and text messages when targeting Israeli entities. It is highly probable that a similarly sophisticated, English-language lure was utilized to compromise the initial Stryker employee.
Privilege Escalation and the Compromise of Entra ID
Gaining a foothold on a single endpoint is insufficient for the scale of destruction Handala achieved. From their initial beachhead, the primary objective was rapid privilege escalation. In the Stryker incident, Handala successfully compromised highly privileged administrative accounts, bypassing existing defensive perimeters, including Multi-Factor Authentication (MFA), to gain deep administrative rights within the company’s core Microsoft environment.
The ultimate prize in this phase of the attack was the acquisition of global administrative access to Stryker’s Microsoft Entra ID (formerly Azure Active Directory). Entra ID serves as the central nervous system for modern enterprise identity, controlling access to cloud applications, internal networks, email servers, and device management platforms. By compromising the central identity hub, Handala essentially acquired the “keys to the kingdom,” granting them unrestricted lateral access without the need to deploy noisy, wormable malware that might be detected by Endpoint Detection and Response (EDR) solutions.
The Weaponization of Microsoft Intune
The most devastating and technically notable aspect of the Stryker breach was the attackers’ weaponization of Microsoft Intune. Microsoft Intune is a cloud-based Unified Endpoint Management (UEM) and Mobile Device Management solution utilized by enterprise IT teams to enforce security policies, deploy applications, and control devices globally from a single, centralized web-based administrative console.
Having secured administrative rights, Handala leveraged the legitimate, built-in functionality of Intune to broadcast highly destructive commands across Stryker’s entire global corporate fleet. Because the commands originated from the trusted MDM platform, they bypassed traditional antivirus and endpoint protections, which are designed to obey administrative directives from Intune.
This methodology yielded catastrophic results:
- Mass Remote Wipe Execution: The attackers issued a synchronized “remote wipe” command targeting all managed endpoints. This resulted in the immediate factory reset of tens of thousands of corporate Windows laptops, servers, and mobile devices across the globe.
- Eradication of BYOD Endpoints: The wipe commands did not discriminate between corporate-owned hardware and personal devices. The commands extended to personal employee smartphones (running both Android and iOS) that were enrolled in Stryker’s “Bring Your Own Device” (BYOD) program via the Intune Company Portal. Personal devices configured with corporate work profiles were maliciously factory-reset, resulting in the collateral deletion of employees’ personal data, photos, and applications.
- Authentication Paralysis and Defacement: To cement the disruption and inflict psychological damage, the attackers defaced the Entra ID login pages. They replaced the standard corporate authentication interface with the Handala logo.
This prevented any un-wiped devices or unaffected personnel from authenticating into corporate services, cloud applications, or communication platforms like Microsoft Teams, effectively blinding the organization.
Forensic Architecture of the Handala Wiper Malware
Concurrent with the MDM-initiated remote wipes, Handala deployed custom destructive wiper malware against Stryker’s servers and proprietary applications that may not have been fully managed by Intune. Unlike ransomware, which encrypts data with the theoretical possibility of decryption upon payment, wiper malware is engineered for absolute, permanent digital eradication.
Forensic analysis of Handala’s wiper capabilities reveals a brutal but highly effective approach to data destruction (categorized under MITRE ATT&CK Technique T1561: Disk Wipe). The malware deployment often begins with the group using AutoIT to inject the wiper payload into a new Windows process. The wiper sometimes initiates with a deceptive message box, falsely claiming to the user that it is installing an update to fix a system issue.
In reality, the malware executes a devastating function designed to overwrite files across the system. The destructive code is specifically programmed to overwrite files with a block of 4,096 bytes of random data. If a targeted file’s size is less than 4,096 bytes, the malware creates a new array to overwrite that specific portion, filling it entirely with zeroes.
This mechanism directly targets and corrupts foundational disk structures, including the Master File Table (MFT) and the Master Boot Record (MBR). By systematically overwriting file headers and structural metadata with random bytes or zeroes, the wiper renders the compromised host completely unbootable. More importantly, it makes the underlying data mathematically and forensically unrecoverable, thwarting data decryption and content recovery efforts even if advanced forensic carving tools are applied.
- Initial Access: Spear-phishing, social engineering, malicious PDF links. Covert foothold established on the enterprise network.
- Privilege Escalation: Compromise of Entra ID (Active Directory) Admin credentials. Unrestricted control over enterprise identity and access management.
- Mass Execution: Microsoft Intune Remote Wipe Commands. Instantaneous factory reset of global laptops, mobile devices, and BYOD endpoints.
- Data Destruction: Custom Wiper Malware (4,096-byte random data overwrite). Corruption of MBR/MFT, permanent data loss, hosts rendered unbootable.
- Psychological Ops: Entra ID login defacement (Handala logo display). Intimidation, confirmation of systemic compromise, prevention of emergency communications.
Data Exfiltration: The Dual-Threat Hack-and-Leak Paradigm
In tandem with the highly visible destructive elements of the attack, Handala publicly claimed to have extracted a massive volume of data prior to executing the wiper sequence. The group asserted that they stole approximately 50 terabytes of critical corporate data from Stryker’s servers.
While Stryker’s official statements indicated an ongoing investigation to assess the full scope, nature, and impacts of the breach, they did not immediately confirm the 50TB theft. However, the dual-threat capability of “hack-and-leak” combined with permanent destruction is a well-documented hallmark of sophisticated state-sponsored actors and Handala specifically. If the exfiltration of 50TB of sensitive corporate data, proprietary engineering schematics for medical devices, and potentially patient-related data is ultimately validated, it introduces severe secondary risks. These include long-term intellectual property theft, massive regulatory penalties under privacy laws, and continued extortion or public leaks designed to further damage the corporation’s reputation.
Operational Disruption and the Anatomy of a “Digital Decapitation”
The immediate operational fallout of the March 11 attack was unprecedented in Stryker’s corporate history, earning the moniker of a “digital decapitation” among cybersecurity analysts monitoring the crisis. The disruption was characterized by its absolute globality, its instantaneous nature, and the sheer totality of the systems compromised.
The Halt of Global IT Infrastructure
Shortly after midnight Eastern Time on Wednesday, March 11, the wiper malware and Intune remote wipe commands were simultaneously executed across the globe. The speed of the disruption was staggering. Within minutes, employees logging in across the United States, Costa Rica, Australia, India, and throughout European offices observed their devices suddenly freezing, rebooting, displaying the Handala logo, and subsequently wiping all local data.
The attack completely and violently severed access to Stryker’s internal networks, email servers, production software, and unified communication tools. Employees attempting to authenticate were met with defaced Entra ID screens or unresponsive, bricked hardware. In response to the unfolding catastrophe, Stryker’s global IT security teams issued emergency directives, urgently advising all 56,000 employees to immediately disconnect from all networks, power down company-issued devices, and refrain from attempting to log in to any Microsoft applications or VPN clients.
Paralyzing the Cork Hub and Global Manufacturing Facilities
The physical, real-world impact of the cyberattack was most acutely felt at Stryker’s primary international manufacturing and engineering facilities. In Cork, Ireland, which houses advanced manufacturing, R&D, and global supply chain operations, the sudden loss of IT infrastructure brought the massive facility to a complete standstill.
Approximately 4,000 to 5,000 employees arriving for their morning shifts, or already operating on the factory floor, found themselves entirely locked out of the digital systems required to operate complex machinery, access product schematics, and coordinate logistics. Because modern medical device manufacturing is intrinsically linked to digital production systems, the inability to access design software and production controls forced Stryker to halt physical activity. Facility managers had no alternative but to send thousands of workers home for the day, as productivity dropped to zero. In certain administrative and operational areas, staff were forced to revert to rudimentary “pen and paper” workflows in a desperate attempt to maintain basic functions—a stark and chaotic regression for a $100 billion advanced technology giant.
The disruption was by no means isolated to Ireland. In their public manifesto, Handala boasted that 79 international offices were forced to shut down entirely. While threat actor claims regarding the exact number of impacted endpoints (claiming over 200,000 systems wiped) are often inflated for psychological impact, corroborating reports from global facilities confirmed a severe, synchronous cessation of business operations worldwide.
The Psychological Toll on the Workforce
Beyond the corporate damage, the attack inflicted a significant psychological toll on the workforce. Employees awoke to find not only their work laptops destroyed but their personal mobile phones—which happened to be connected to the corporate Wi-Fi or enrolled in the Intune company portal—factory reset. The loss of personal photos, contacts, and private applications due to a geopolitical cyberattack against their employer created widespread confusion, frustration, and a profound sense of violation among the staff, further complicating the company’s internal crisis management.
Economic, Regulatory, and Financial Repercussions
The financial markets and federal regulatory bodies reacted swiftly to the unprecedented disruption of a major healthcare infrastructure provider. The incident highlighted the immediate financial materiality of destructive cyber warfare.
Market Volatility and Shareholder Value Destruction
News of the cyberattack initially broke via social media reports from confused employees whose devices were wiped, and was subsequently confirmed by major financial outlets, including The Wall Street Journal. The market reaction was immediate and punitive. Stryker Corporation’s stock (NYSE: SYK) experienced a sharp decline, falling between 3.4% and 4.6% during Wednesday’s trading session following the news.
This sudden drop in shareholder value reflected acute investor concern regarding several compounding factors: the immediate loss of revenue due to halted global production, the exorbitant anticipated costs of forensic recovery and hardware replacement for thousands of devices, and the potential long-term reputational damage to the company’s standing as a reliable, secure supplier of life-critical medical technologies.
SEC Disclosures and Materiality Under New Cyber Rules
In compliance with stringent cybersecurity disclosure regulations recently enacted by the U.S. Securities and Exchange Commission (SEC), Stryker rapidly filed a Form 8-K to report the material event. The company formally disclosed that it had identified a cybersecurity incident resulting in a “global disruption to the company’s Microsoft environment” that impacted certain information systems and business applications.
In its official statements and SEC filings, Stryker’s executive management emphasized several critical points regarding the crisis:
-
Containment and Investigation: The company immediately activated its cybersecurity response plan, engaging external advisors and cybersecurity experts (specifically noting the involvement of Microsoft engineers) to investigate, assess, and contain the threat.
- Absence of Ransomware: Stryker explicitly noted to the SEC and the public that there was “no indication of ransomware or malware” (referring to traditional extortion malware), confirming to analysts that the incident was a purely destructive wiper attack rather than a financially motivated extortion attempt.
- Uncertain Recovery Timeline: The company transparently acknowledged that the “full scope, nature, and impacts—including operational and financial effects—are not yet known,” and critically, that the timeline for full system restoration remained completely indeterminate.
Financial and Regulatory Timeline
| Details | Information |
|---|---|
| Date of Incident | March 11, 2026 |
| Market Reaction | SYK stock drops ~3.4% - 4.6% on the day of the attack |
| Regulatory Action | Filing of SEC Form 8-K disclosing global Microsoft environment disruption |
| Company Stance on Extortion | “No indication of ransomware or malware” |
| Recovery Estimate | Timeline for full restoration unknown; impacts not fully quantified |
Historical Context: Prior Cyber Incidents
This devastating wiper attack follows a prior, unrelated data breach disclosed by Stryker in 2024. In that historical incident, an unauthorized party accessed the corporate network between May 14 and June 10, 2024, compromising sensitive consumer data including names, medical information, and dates of birth. Stryker filed a notice of that data breach with the Attorney General of Texas on December 5, 2024, and notified affected individuals. Additionally, the company has historically dealt with product-specific vulnerabilities, including responses to the WannaCry ransomware campaign and KRACK wireless protocol flaws affecting their connected hospital beds.
While the 2024 incident was a traditional data exfiltration and privacy event, the 2026 Handala wiper attack represents a monumental, unprecedented escalation in the severity of cyber threats facing the organization, shifting from data privacy concerns to existential operational survival.
The Grueling Logistics of Enterprise Recovery
The road to recovery following a massive, enterprise-wide wiper attack is fundamentally different—and significantly more arduous and expensive—than recovering from a standard ransomware event. In a ransomware scenario, organizations face a binary choice: negotiate and pay for a decryption key, or restore from backups. In a wiper attack, the data is permanently eradicated; there is no key to purchase.
Rebuilding an enterprise network of Stryker’s magnitude from the ground up requires a painstaking, serialized process. Every affected endpoint—amouting to tens of thousands of laptops, servers, and mobile devices—must be individually wiped, manually re-imaged, physically verified, and subjected to rigorous security checks before being permitted to rejoin the corporate network.
Cybersecurity experts project that this scale of infrastructural rebuilding will require weeks, if not months, to fully execute, incurring massive operational costs and requiring thousands of hours of IT labor. During this protracted recovery period, Stryker is forced to lean heavily on business continuity plans to support clients and partners, operating in a degraded state while the digital foundation is reconstructed.
Healthcare Infrastructure and Medical Supply Chain Implications
Upstream Paralysis and Just-in-Time Vulnerabilities
While the Handala attack targeted Stryker’s corporate IT infrastructure rather than hospital networks directly, the healthcare ecosystem relies on a highly optimized, “just-in-time” supply chain. Modern hospitals and surgical centers maintain limited on-site inventories of specialized orthopedic implants, neurotechnology devices, and surgical consumables to reduce overhead costs. They depend absolutely on manufacturers like Stryker to rapidly process orders, manufacture components, and distribute them precisely when scheduled surgeries dictate.
With Stryker’s global network, manufacturing facilities (like Cork), and ERP systems rendered completely offline, the capacity to process new hospital orders, coordinate global shipping, and manage logistics is severely bottlenecked, if not entirely frozen. Prolonged outages at the manufacturing level inevitably lead to delays in the output of essential surgical tools, artificial joints, hospital beds, and emergency medical equipment.
Risks to Clinical Operations, Device Maintenance, and Patient Safety
Although initial reports indicated no immediate, direct disruption to hospital operations or the active functionality of patient care equipment (such as deployed defibrillators or hospital beds currently in use), cybersecurity analysts and healthcare executives warn that the downstream impacts will inevitably manifest as the outage persists.
- Software and Security Patches: Advanced connected medical hardware, such as the Mako robotic surgical systems, requires continuous software updates, performance calibrations, and cybersecurity patches from the manufacturer. An incapacitated vendor cannot distribute these critical updates, potentially leaving deployed hospital equipment vulnerable to separate, opportunistic cyber threats.
- Technical Support and Maintenance: Hospitals rely on Stryker’s engineering teams for real-time technical support, troubleshooting, and routine device maintenance. The severance of communication channels leaves clinical staff without critical vendor assistance during complex procedures or hardware malfunctions.
- Procedure Delays and Surgical Triage: A sustained disruption in the supply chain for orthopedic implants, specialized screws, or surgical consumables will inevitably force hospitals to triage care, delaying elective and non-emergency surgeries. This impacts patient care timelines, prolongs suffering, and disrupts hospital revenue streams.
The attack forcefully demonstrates that medical device manufacturers constitute critical national infrastructure. A digital strike against a Tier-1 vendor like Stryker is, by proxy, a strike against the thousands of healthcare systems and millions of patients that depend upon them. Federal authorities, including the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI, closely monitor such incidents precisely because of these cascading impacts on public health.
Comparative Historical Analysis: Echoes of NotPetya
To accurately contextualize the severity, methodology, and impact of the Stryker breach, cybersecurity historians and analysts inevitably draw parallels to the devastating NotPetya attack of June 2017.
NotPetya, attributed by international intelligence agencies to the Russian military intelligence agency (GRU), was nominally targeted at Ukrainian infrastructure but rapidly proliferated globally, crippling multinational corporations such as the Danish shipping behemoth A.P. Møller-Maersk. Like the Handala attack on Stryker, NotPetya was a destructive wiper malware masquerading as ransomware. It generated over $10 billion in global damages by irreversibly encrypting master boot records, offering no actual decryption mechanism even if a ransom was paid.
The similarities between NotPetya and the Stryker incident are striking and instructive:
- Geopolitical Motivation: Both attacks were born out of regional geopolitical kinetic conflicts (the Russo-Ukrainian War for NotPetya; the escalating US-Israel-Iran conflict for Stryker).
- Destructive Intent: Both utilized wiper malware to maximize operational damage, data destruction, and economic disruption rather than seeking direct financial extortion.
- Global Supply Chain Impact: Both attacks crippled essential nodes in global supply chains (global shipping and logistics for Maersk; global healthcare infrastructure and medical devices for Stryker).
Comparative Analysis
| NotPetya | Handala / Stryker | |
|---|---|---|
| State Sponsor | Russia (GRU) | Iran (MOIS / Void Manticore) |
| Geopolitical Catalyst | Russo-Ukrainian Conflict | US/Israel strike on Minab, Iran |
| Malware Type | Wiper (disguised as ransomware) | Pure Wiper (4096-byte overwrite) |
| Primary Target Sector | Ukrainian infrastructure, Global Shipping (Maersk) | US/Western Healthcare Infrastructure (Stryker) |
| Propagation Method | EternalBlue (SMB exploit), M.E.Doc update | Weaponization of Cloud Identity (Entra ID) and MDM (Intune) |
| Primary Impact | MBR Encryption, unrecoverable data | MFT/MBR Corruption, unrecoverable data, mobile device wipes |
However, the Stryker incident signifies a critical evolution in threat actor methodology over the intervening nine years. Whereas NotPetya relied on a leaked NSA exploit (EternalBlue) to worm its way laterally across unpatched on-premises networks, Handala achieved rapid, global propagation without needing a traditional network worm. Instead, they captured the enterprise’s central nervous system: the cloud-based identity and endpoint management platforms (Entra ID and Intune). This evolution indicates that modern attackers no longer need to rely on complex exploits to traverse a network; instead, they simply need to compromise the highly privileged administrative identities that govern the network from the cloud.
Strategic Insights and Cybersecurity Paradigm Shifts
The Stryker cyberattack provides several profound second and third-order insights into the shifting landscape of enterprise cybersecurity.
The incident serves as a harsh, real-world stress test for currently prevailing IT architectures, revealing systemic vulnerabilities that demand immediate strategic remediation across all critical infrastructure sectors.
The Peril of Centralized Cloud Management as a Single Point of Failure
Over the past decade, enterprise IT has heavily migrated toward centralized, cloud-based Unified Endpoint Management (UEM) and Identity and Access Management (IAM) solutions. Platforms like Microsoft Intune and Entra ID are championed for enforcing zero-trust policies, streamlining global administration, and ensuring compliance. While these tools offer immense operational efficiency, the Stryker incident brutally demonstrates that they also introduce an existential single point of failure (SPOF).
When a sophisticated attacker successfully compromises a Global Administrator account within these cloud platforms, the entire security architecture inherently works against the defender. The very mechanisms designed to secure the fleet—the ability to push software updates, enforce strict access policies, and remotely wipe lost or compromised devices—are inverted by the attacker to execute mass destruction seamlessly. Because the commands originate from the trusted management plane, endpoint security tools do not block them.
The attack underscores the urgent necessity for enterprises to implement strict compartmentalization and blast-radius limitations within their cloud environments. Organizations must transition away from standing global administrative privileges. Instead, they must mandate multi-person authorization (quorum approvals) for highly destructive commands, such as tenant-wide remote wipes or massive policy changes, to prevent a single compromised identity from executing a digital decapitation.
The Inherent Liability of BYOD Policies
The extensive collateral damage inflicted upon Stryker employees’ personal devices brings the inherent risks of “Bring Your Own Device” (BYOD) policies into sharp, uncomfortable focus. While MDM solutions technically allow organizations to partition corporate data from personal data on a single device through work profiles, the centralized wipe command executed by Handala resulted in the complete factory reset of countless personal smartphones.
This dynamic generates significant secondary fallout for the corporation. Beyond the operational halt of the business, the permanent destruction of employees’ personal data—family photos, private communications, local unbacked-up applications—deeply fractures employee trust and decimates morale during a crisis.
Furthermore, it introduces incredibly complex legal, privacy, and Human Resources liabilities regarding the extent of corporate control, overreach, and responsibility over personal hardware. Future BYOD architectures must be re-evaluated; organizations must either provide dedicated corporate hardware to air-gap risk or ensure that MDM implementations inherently firewall corporate wipe commands from interacting with the base operating system of employee-owned devices under any circumstances.
Redefining Resilience Against Purely Destructive Malware
The healthcare manufacturing sector, like many others, has largely built its incident response playbooks and cyber insurance models around the threat of ransomware. Traditional ransomware playbooks involve containment, legal assessments regarding extortion payments, negotiation strategies with threat actors, and the procurement of decryption keys.
The Stryker incident necessitates a fundamental paradigm shift: organizations must explicitly prepare for purely destructive warfare. When threat actors are motivated by geopolitical retribution, ideological hatred, or state-sponsored disruption rather than financial gain, deterrence through negotiation is impossible. In this threat model, true resilience relies exclusively on the isolation, integrity, and speed of offline, immutable backups.
If an organization’s backups are connected to the primary Active Directory domain or are accessible via the compromised cloud identity tenant, they will inevitably be targeted and wiped alongside the primary data. Organizations must ensure that disaster recovery architectures are entirely decoupled from the primary identity provider. This requires utilizing air-gapped infrastructure or cryptographically immutable storage arrays to guarantee that core enterprise data survives a systemic, credential-based wiper event.
The Blurring of Cyber and Kinetic Warfare
Finally, the Stryker case study cements the reality that the private sector is now an active, primary theater in international geopolitical conflicts. Security analysts accurately note that attacking a high-profile U.S. healthcare manufacturer creates “outsized strategic and political ripple effects,” serving as an effective, asymmetric pressure point in international relations.
Multinational corporations can no longer view cybersecurity merely as a technical compliance issue managed solely by the IT department; it must be elevated and managed as a core geopolitical business risk by the board of directors. Companies operating within critical infrastructure sectors must continuously align their cyber threat intelligence with global geopolitical developments. They must anticipate that international kinetic events—such as military strikes, sanctions, or diplomatic breakdowns—may precipitate immediate, severe cyber retaliation against their corporate assets, even if they have no direct involvement in the conflict.
Conclusion
The March 11, 2026, cyberattack on Stryker Corporation stands as a defining watershed moment in the intersection of geopolitical cyber warfare and global healthcare infrastructure. By masterfully weaponizing the corporation’s own centralized identity and endpoint management tools—specifically Microsoft Entra ID and Intune—the Iran-linked Handala Hack Team executed a highly efficient “digital decapitation.” The deployment of custom destructive wiper malware successfully erased hundreds of thousands of devices, permanently destroyed data, and brought a $100 billion multinational enterprise to a functional, chaotic halt.
The immediate disruption of Stryker’s global manufacturing hubs, particularly the paralysis of the massive Cork facility in Ireland, underscores the acute vulnerability of modern, digitally integrated medical supply chains. While the attack successfully decimated corporate IT networks, its true peril lies in the downstream implications for global medical supply availability, threatening the logistical delivery of critical surgical equipment, orthopedic implants, and the continuous maintenance of advanced clinical technologies upon which hospitals rely.
Ultimately, the Stryker incident is a clarion call that demands a structural reevaluation of enterprise security architectures worldwide. It ruthlessly exposes the existential risks inherent in centralized cloud administration and highlights the catastrophic potential of geopolitical conflicts spilling into the private sector. To survive the rapidly evolving landscape of destructive, asymmetric cyber warfare, critical infrastructure organizations must fundamentally transition from a posture of mere perimeter defense to one of absolute systemic resilience, ensuring that their foundational data and operational continuity can withstand the absolute compromise of their digital environment.